How to remove ransomware the right way: A step-by-step guide (Updated for 2019)

Ransomware is the number one malware threat to home and business users alike. We’ve seen sophisticated variants using slick presentations and payment portals akin to modern start-ups and recently a variant disguised as a wiper. Regardless of the variant, all ransomware infections have two things in common: locked files and a ransom payment demand.
So we’ve created this step-by-step article to guide you through the process of what to do should you be infected by ransomware.
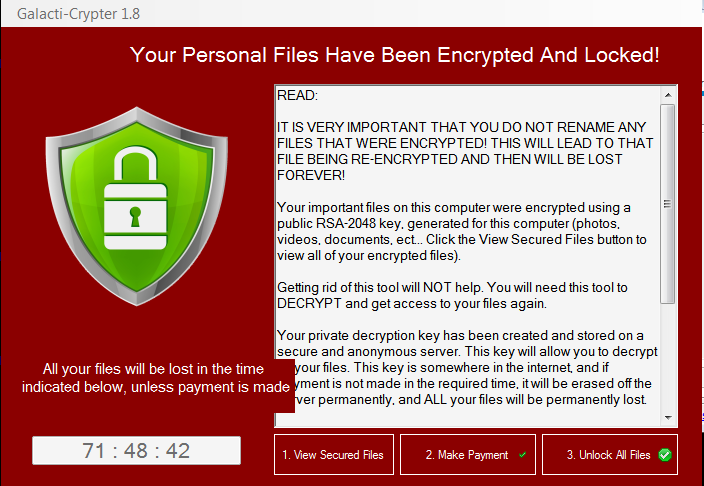
Galacticypter GUI Courtesy of MalwareHunterTeam
So what exactly is ransomware?
Ransomware is a type of malicious software that locks up your files and demands a ransom to access them. This form of malware is now the most lucrative form of cybercrime as victims feel threatened to pay, even if there are no guarantees of getting the data back.
Should I pay the ransom?
It depends. Paying ransom should be considered a last resort. You have several options, depending on your situation, type of ransomware attack, etc.
Particularly for larger enterprises, paying up immediately seems like the best option to recover files and avoid the potential embarrassment of admitting a security breach or inadequate IT security measures. Yet, in many cases, even after paying large sums of money users still don’t receive their files. It’s best to weigh in all your options first before deciding to pay the ransom.
We’re here to help. No strings attached.
Emsisoft is a proud associate partner of No More Ransom, an initiative by the National High Tech Crime Unit of the Netherlands’ police, Europol’s European Cybercrime Centre, and other cybersecurity companies. Our shared goal is to help victims of ransomware retrieve their encrypted data without having to pay.
Emsisoft fights ransomware on the front-line daily, which means we are best positioned to offer you free, easy-to-follow advice with no strings attached. So let’s begin.
I’ve been infected with ransomware! What should I do?
Here is a word from our Chief Technology Officer and Head of the Emsisoft Malware Research Lab, Fabian Wosar:
“Ransomware infections are unique in many ways. Most importantly, a lot of the natural instincts, which are usually correct when dealing with malware infections, can make things worse when dealing with ransomware.”
So, take a breath and follow these steps:
1. Isolate infected systems
The first step in the recovery process is to determine the extent of the incident and isolate the impacted systems. Ideally, the impacted network should be taken offline completely; if this is not immediately possible, disconnect all affected devices from the network (e.g. by unplugging the relevant ethernet cables and/or removing the devices from the Wi-Fi). Ransomware operators commonly monitor the network for signs of mitigation activity, so be sure to coordinate your efforts and use out-of-band communications to avoid alerting threat actors that remediation is underway.
2. Disable any system optimization and cleanup software
A lot of ransomware strains store themselves, and other necessary files, in your Temporary Files folder. If you use system cleanup or optimization tools like CCleaner, BleachBit, Glary Utilities, Clean Master, Advanced SystemCare, Wise Disk/Registry Cleaner, Wise Care, Auslogics BoostSpeed, System Mechanic, or anything comparable, you need to disable these tools immediately.
Action: Check to make sure there are no automatic runs scheduled. Otherwise, these applications may remove the infection or other necessary ransomware files from your system. We will require these later to determine which type of ransomware you have been infected with.
3. Create an image or backup of the system
Some ransomware strains have hidden payloads that will delete and overwrite all encrypted files after a certain amount of time has passed. Decryptors may not be one hundred percent accurate, as ransomware is often updated or simply buggy and may damage files in the recovery process. In these cases, we have found that an encrypted backup is better than having no backup at all.
Action: This is an important step – create a backup of all of your encrypted files before doing anything else.
Additional resource: Detailed advice on how backups prevent ransomware.
4. Quarantine, but don’t delete!
Your anti-malware solution may have already quarantined the infected file. That’s ok! But, do not delete any files. To figure out what exactly the ransomware has done to your computer, we will require the ransomware to be executable.
Note: It is fine to disable the infection by disabling any autorun entries pointing to it or by quarantining the infection. However, it is important not to delete it from quarantine or to remove the malicious files right away without a complete backup.
To identify a strain of ransomware, we will need access to the malicious file. Additionally, it can be helpful to see a sample encrypted file (ideally nothing sensitive, such as a system icon or similar) to identify exactly which encryption method was used and if any identifiable features match known strains of ransomware.
5. Reset credentials
There’s a high chance that threat actors have been able to harvest various credentials from your organization. To reduce the risk of re-compromise post-recovery, it’s important to reset any passwords that may have been affected during the incident, particularly for administrator accounts and credentials relating to remote services and high-value assets and data repositories. Be careful that you don’t lock yourself out of systems that will be needed later in the recovery process.
6. Triage-impacted systems
After impacted systems have been isolated and images have been made, it’s time to triage the impacted systems. When it comes to recovery, prioritize the systems that are most important for the organization to return to normal operations. Recovery prioritization is something that should be included in your incident response plan; systems may be prioritized based on a range of factors, including revenue generation, health and safety, data sensitivity, industry regulations, and so on.
Note: Before restoring from a backup, you must verify that it is free from any malware.
Action: Organizations of all sizes should make an incident response before an incident occurs. This incident response guide is a good starting point (it’s written for MSPs but most of the principles apply to all organizations!).
7. Identify the type of ransomware and check decryptor availability
If your system is infected but doesn’t know what type of ransomware you have been infected with, visit the Emsisoft Decryption Tools page to identify the ransomware strain and check if a decryptor is available.
Once you know which type of ransomware you have been infected with and a decryptor is available, go ahead and start unlocking your files.
We work tirelessly to ensure the most up-to-date decrypters are listed here. However, please be aware that there is no guarantee that the decryptor you require will be available. Ransomware evolves and more variants are added every day.
If you have the decryptor you require, follow the instructions provided on the download page to execute the program.
Action: Go to the Emsisoft Ransomware Decryption Tools page to identify the ransomware strain and check decryptor availability.
Additional resource: If you would like to learn more about how security researchers identify ransomware, see this interview with security researcher Michael Gillespie.
8. Investigate, learn and harden
To reduce the risk of a future incident, it’s important to thoroughly investigate what went wrong. What was the entry point? Which tools were used during the attack? How long were threat actors on the system? How did threat actors evade your security processes? Insights gathered during the post-mortem can be used to bolster security protocols, resolve vulnerabilities and improve response procedures.
Additional resource: Emsisoft EDR is a valuable tool for gaining insight into the origin of an attack.
Bonus: Note for server victims: identify the point of entry and close it
Recently, we have seen many cases of compromised servers. Ransomware accesses the server by brute force. User passwords are rapidly fired at the server via Remote Desktop Protocol (RDP).
We firmly suggest you check your event logs for a large number of login attempts fired in quick succession.
If you find such entries or if you find your event log to be completely empty, your server was hacked via RDP. It is crucial that you change all user account passwords immediately. We also suggest disabling RDP if at all possible.
Action: check all the user accounts on the server to make sure the attackers didn’t create any backdoor accounts that would allow them to access the system later.
Additional resource: See this guide for more information on how to secure RDP from ransomware attackers.
Emsisoft Enterprise Security + EDR
Robust and proven endpoint security solution for organizations of all sizes. Start free trialConclusion
It’s important to note that ransomware attacks can vary in terms of impact and complexity. While this basic guide can be considered a good starting point, successfully remediating a complex ransomware incident can be challenging and in many instances external incident response specialists may need to be called in.