Metadata and Mobile Security

 Ever since Edward Snowden blew the whistle on the NSA’s controversial monitoring tactics of US citizens, the tech media landscape has sustained an ongoing narrative on digital privacy. No doubt, this conversation has by now achieved a global reach and is taking place in a number of languages besides English. Countries the world around have security agencies, and with the advent of instantaneous, transcontinental communication personal digital privacy is an issue that transcends national borders.
Ever since Edward Snowden blew the whistle on the NSA’s controversial monitoring tactics of US citizens, the tech media landscape has sustained an ongoing narrative on digital privacy. No doubt, this conversation has by now achieved a global reach and is taking place in a number of languages besides English. Countries the world around have security agencies, and with the advent of instantaneous, transcontinental communication personal digital privacy is an issue that transcends national borders.
There is one term that still requires translation though, regardless of your mother tongue: Metadata.
Metadata Defined
In so many words, metadata is data about data. Within the context of the global conversation on personal privacy, metadata is being used to refer to information that reveals the generic conditions of a transaction rather than the specifics. For those of you who don’t speak legalese, that means, for example, the length of a phone conversation and the phone numbers involved, as opposed to the actual, spoken-word content of the call. Back in June 2013, US President Barrack Obama stressed that the NSA only monitors civilian metadata and implied that this was harmless; however, a new study by Stanford University has labeled metadata highly sensitive material and the NSA’s metadata monitoring highly unconstitutional. The researchers’ reasoning is simple: mobile phone numbers can be linked to individuals and the phone numbers dialed by these individuals can reveal sensitive personal information.
For example, a call log that looked like this:
555-555-1234
555-555-3456
555-555-5678
Might not look like much. But if a simple search on Google Places or Yelp connected those phone numbers to places like this:
555-555-1234 – Gun and Ammo Shop
555-555-3456 – Pilot Training School
555-555-5678 – Local Mental Institution
Prying eyes at the NSA might be tempted to further investigate the identity linked to said call log.
Mobile (Metadata) Security
While the above example is indeed an exaggeration, metadata can be revealing no matter who you are or where you’re calling. Metadata can help prying eyes reveal the most intimate details of your life. For example, if you called a hospital or clinic someone with your metadata could infer that you were sick. If on the other hand you called a phone number linked to a financial institution, someone with your metadata could make inferences about your financial situation – like where you bank, where you hold credit cards, and whether you are in debt. On an even more personal level, metadata could even reveal your political or religious affiliations, provided you had called your local representative or church.
Not surprisingly, the political debate surrounding the NSA’s use of metadata is intense, and it has even extended to police search and seizure rights in the US Supreme court. Police with physical access to confiscated mobile devices have access to the arrested’s call logs and internet search histories, as well as more specific information like emails and texts. Many feel this is an intrusion of personal rights. Regardless of one’s legal interpretation of the matter, what’s probably most important is that metadata has serious implications in the realm of identity theft.
A Stolen Smartphone is a Stolen Life
There is quite the buzz surrounding governmental use of mobile metadata. As a consequence, many people forget that mobile metadata can also be used by identity thieves and that acquiring it is even easier than stealing information from a PC. The reasons are simple.
- Mobile devices are smaller than PCs; this makes them easier to physically steal and more likely to be left behind in public.
- Many mobile devices are not password protected, and those that do use passwords can still be hacked.
If you’re deleting your Internet browsing history and the majority of your sensitive emails and texts on a regular basis, you may indeed think that your mobile device is secure. But this is not entirely correct. Determined identity thieves have many tricks up their sleeves, and your device’s metadata combined with the thief’s favorite search engine could be all that is needed to unravel the details of your life through inference – just as is done by the NSA.
On top of this, one must also realize that physical access to a stolen smartphone provides direct access to much more than metadata, just as it does in the contentious case of police search and seizure. This is because most of us simply do not have the time to obsessively delete everything we do on our smartphones, and most of us use our smartphones (and tablets) to do quite a lot. Worst case scenario: an unsecured mobile device that’s never been cleared is a window into someone else’s life and mind – and to ID thieves looking for an easy score that window is paned with gold.
Emsisoft Mobile Security’s Anti-Theft Feature
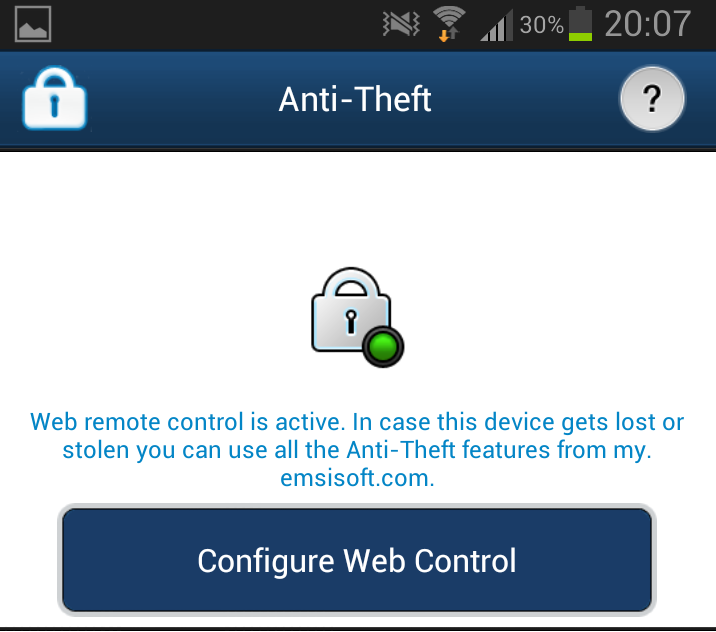
Emsisoft Mobile Security has been designed to protect your Android device from mobile malware. As an added benefit, it also includes an Anti-Theft feature that allows you to lock or completely wipe all data and metadata from your device if it is stolen, through my.emsisoft.com.
We have included Anti-Theft to help users protect their personal, digital privacy as best they can. We hope that most of our users will never be targeted by intrusive search warrants or the NSA, but we know that anyone can have their mobile device stolen. Our hope is that Emsisoft Mobile Security can help promote a more digitally secure world and prevent cases of physical theft from extrapolating into theft of your identity.
Governmental monitoring of sensitive (meta)data may indeed be beyond the control of any one company or individual, but every action we take to spread identity theft awareness counts. And though Emsisoft may indeed be committed to the vision of a Malware-Free World, an Identity Theft-Free planet would be pretty nice too.
Emsisoft Enterprise Security + EDR
Robust and proven endpoint security solution for organizations of all sizes. Start free trialHave a Great (Malware-Free) Day!