Botnets: Dawn of the connected dead


It seems everything is connected these days. Toasters, baby monitors, even coffee machines have access to the internet. Almost toylike for adults, these devices are created to make your life easier, fun even. But convenience for you can also mean easy access for cybercriminals.
Imagine a child surrounded by toys he has stolen from as many other kids as he was able. Each of these little toys laid in a neat order on the floor has the name of someone written on its foot. Its owner may have not even noticed that their toy is missing, yet now it is a player in the world this bully of a child has created.
When the bully is in control of all of the toys, he can make them do whatever he wants. A botnet works much the same way. The botmaster (the child) controls all of the devices (toys). He can use them to carry out illegal activity and worst of all, because he is using your toys to do it, he is anonymous.
Botnets have been used to spread spam and overload websites to cause them to crash, leading to financial damage for businesses (DDoS attacks).
It could come as a shock to you to know that your computer at this very moment may be sending spam email, distributing child pornography or helping to crash Twitter’s servers in a bid to take them offline.
Many of your internet capable devices could be part of a bot army.
Never fear. There are clear indicators that your computer has joined the scummy ranks of the internet and is now a toy in the hands of a cyber bully.
In today’s post we will explain what botnets are, how botnets are used for criminal gain and how you can keep your toys out of the hands of botmasters.
Let’s get to it.
What is a botnet?
To explain this, first, let’s look at what a bot is.
A bot is installed by a type of trojan, a form of malware hiding in your operating system waiting idly by for instructions from a command and control server that is controlled by a criminal, known as a botmaster or bot herder. Bots can perform a wide variety of automated tasks on behalf of their master, such as sending phishing scam emails or running keyloggers to collect credit card details. All while the cybercriminals benefiting from this illegal activity are safely located somewhere far across the Internet.
A botnet uses your computer along with thousands of other devices meaning the cybercriminals at the wheel can harness almost unlimited computing power. Instead of sending 100 spam emails from one computer, they can send 10 from 200,000 computers. It has no impact on your system while giving them endless reach. Bots can even camouflage their processes and run other masking tasks such as turning off your anti-malware, all without your knowledge.
Due to the bot’s connection to the internet it is also able to infect hundreds if not thousands of new computers rapidly while still performing whatever task it has been allocated.
Bots are not always computers either. Any internet capable device is able to be infected. CCTV cameras are notoriously hijacked for this very purpose.
One infected device is a bot (robot). A collection of these bots forms a botnet (robot network).
How does a botnet work?
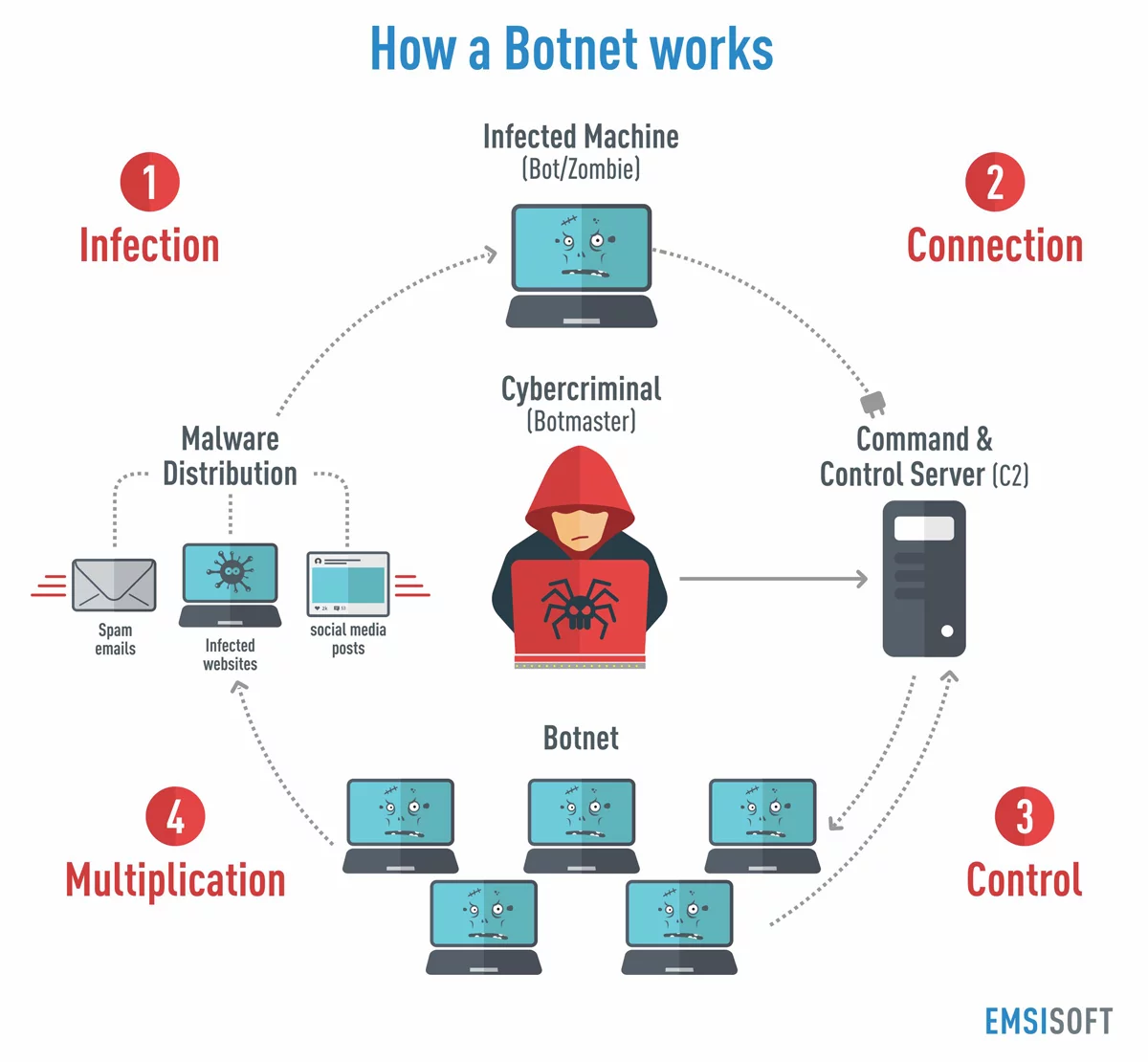
Like any malware infection, there are specific stages to a bot infection, from getting into your system, to communicating with the botmaster and executing tasks. They are best broken down as follows:
- Infection
The botmaster sends out malware to infect computers. These can get into your computer through drive-by downloads, suspicious email attachments or links in social media posts. The bot malware will exploit vulnerabilities in your software, looking for backdoor access via your outdated plugins or an out of date operating system. It will then take root in your system.
- Connection
Once in your system, the malware will use the internet to make contact with the command & control server (C2). Your computer will remain idle at this stage and the bot dormant, except for periodically checking for instructions from the botmaster. As the system impact is so slight, you will have no idea this is happening.
- Control
The botnet as a whole may lay dormant for some time while waiting for a task to be performed. Once the botmaster has a purpose for the botnet, he/she sends instructions to the bots via the command & control server. It is at this stage that the botnet booter awakens and starts carrying out malicious activities such as sending spam emails or taking part in a DDoS attack.
- Multiplication
In the meantime, the botmaster will be focussed on recruiting more and more computers to expand the botnet. As these computers don’t appear to be doing anything, the botnet could contain hundreds of thousands of zombie computers without raising any suspicion at all.
Uses for botnets
Botnets act as a proxy server for illegal activity without ever revealing the perpetrator. The spread of illegal activity over thousands of devices conceals the source of the crime while providing almost unlimited computing power to the cybercriminal. This can be wielded to:
-
- Commit advertising fraud. Thousands of computers can be harnessed to repeatedly click on ads, raising generous profits for fraudsters who utilise ad-clicks to make money.
- Download and distribute illegal materials such as child pornography or just generally spam people online. Companies will pay big money to have their ads spread as far and wide as possible. Renting a botnet or hiring a business with access to one is the easiest way to achieve this.
- Mine Bitcoin to make someone else rich by spreading the workload over thousands of bots.
- Steal your private data including passwords and credit card details through the use of keyloggers.
- Commit a botnet DDoS attack and overload and crash an online service such as Twitter or Spotify.
- Send spam emails to phish for the credit card details and private information of new victims.
- Spread ransomware to new victims via email attachments.
- Conduct polling fraud with a botnet can hugely influence an outcome as each computer counts as one unique vote.
- Brute force attack business servers to figure out a password and gain access to a major business network.
You may be thinking that this has nothing to do with you. That there is no possible way that your computer could be one of a few thousand.
But, did you know the Zeus botnet consisted of 3.6 million bots in the US alone?
Currently a quarter of the world’s population access Facebook every month, a popular infection source for Zbot (Zeus) and other malware. It is more than likely at least one of your devices could have come into contact with one of these bot malware strains.
Remember, this does not only affect your computer. All internet capable devices are vulnerable. Like that time a series of smart toasters, DVRs and other web-enabled devices broke the internet, taking down Amazon, The New York Times, Netflix and many other services we live our lives by.
It is a particularly scary thought that it’s possible for complete beginners to create a botnet in less than 15 minutes in the comfort of their own home. Imagine what the sophisticated minds of today’s hackers could do with unlimited resources; including your fridge or home PC.
This affects everyone. If your computer conducts illegal activity, ignorance is not an excuse. If the illegal behavior comes from your computer you are responsible.
Strength in numbers: noteworthy botnet attacks
One of the key benefits for attackers is that using a botnet conceals their identity. This enables larger scale attacks with minimal consequence for the botmaster. Here are some notable recent examples:
- Mirai botnet
The name Mirai comes from the Japanese language and means ‘the future’. It is believed to have come from an anime series named Mirai Nikki.
Mirai works by continuously scanning the internet for IP addresses of Internet of Things (IoT) devices. While scanning it identifies vulnerable gadgets and logs into them. Once inside, it infects them with Mirai malware.
Just like a bot on your computer, Mirai malware operates on your device with very little system impact.
The Mirai botnet has been used for some the largest scale DDoS attacks in recent years, including:
- The September 2016 attack on the security blog Krebs on Security.
- The attack on French webhost OVH, the largest ever seen, also utilized the Mirai botnet.
- The October 2016 attack, where DNS service provider Dyn was targeted. This botnet attack had such an impact that it took Twitter, Amazon, Netflix, AirBnB and Reddit offline. Liberia’s entire internet infrastructure was also targeted in this attack.
Each new Mirai attack has become the largest of its kind ever recorded, and it continues to recruit devices to its botnet army.
- Hajime botnet
There are claims that the Hajime botnet was created as direct competition for Mirai.
First discovered in October 2016 by Rapidity Networks, Hajime has attempted to seek out as many bots as possible. The sign-off notes left behind claim that the only objective of Hajime is to neutralise IoT devices before Mirai or any other botherder can get access to them.
However some security experts question whether Hajime really is a white hat operation, claiming that while it does close ports to Mirai, it opens others for itself.
Hajime already controls more than 300,000 infected devices, mostly DVRs, routers and internet-connected cameras, but is not currently used for any malicious activity. The concern is that if this botnet is hijacked, who knows what it could be used for.
- Zeus/Zbot botnet
Zeus spreads in the same way as Mirai and has been doing so for years. The trojan of choice for stealing banking details, it works via a man-in-the-browser keylogger attack, taking in all of your internet banking and credit card details.
It has also been used to trick every-day PC users into thinking their computer is infected with some other type of virus via tech support scam popups.
At the height of its activity, Zeus compromised Bank of America, NASA, ABC, Cisco and Amazon. Before Mirai it was the largest botnet of its kind, but instead of performing DDoS attacks, it spread the CryptoLocker Ransomware.
Did you know that once you have become infected with bot malware you can remain infected forever?
If the impact on your computer is so difficult to detect, how can you ever know that this malware has taken root in your system? Don’t worry. There are clear signs.
Symptoms of a botnet infection
There are ways to tell if your computer has suddenly been recruited to a botnet army. Keep an eye out for the following:
System speed slows suddenly
If your device has suddenly slowed to zombie speeds, it may be that your system is too busy executing commands issued by an attacker to complete your usual tasks. Take a look at your Task Manager and see what’s going on. If you can’t see any processes that explain your system lag, you may need to look a little deeper. Check what is running in the background and if you are hosting unwanted data on your system.
Unexplained system volume changes
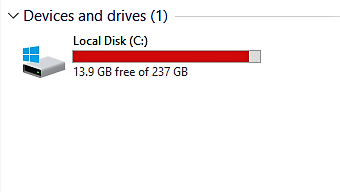
Similarly, check your hard drive space. Have you suddenly lost volume without reason? This could be because a hidden host is using up this space and concealing itself.
Checking your hard drive involves three very simple steps:
- Open File Explorer. You can use the keyboard shortcut, Windows key + E or tap the folder icon in the taskbar.
- Tap or click This PC from the left window.
- You can see the amount of free space on your hard disk under the Windows (C:) drive.
 Sudden web browser or email issues
Sudden web browser or email issues
Does your web browser crash often for no reason? Are you receiving bounced return mail that wasn’t sent by you in the first place? These are all possible signs that your computer is being used for purposes you are unaware of.
Easy botnet detection: prevent infection
Preventing botnet malware is just like preventing any other type of malware and because it is so difficult to remove once it is in your system, prevention is your only real defense. Follow these simple steps to keep trojans out.
For PC
- Regular software updates are vital. Be sure to keep your operating system and applications up to date as part of your regular computer spring cleaning.
- Think before you click. Don’t open mail attachments from senders you don’t recognise (or attachments from sender you do recognise but didn’t ask for). Similarly, be wary of any email asking you to click on a link. Educate yourself on the typical ways phishing scams get your information and plant malware.
- Use a quality Anti-Malware suite to keep zero day threats at bay.
For other internet capable devices
- Don’t set and forget. Many of the products we receive are set with default passwords. These include wifi routers which can be accessed very quickly if you don’t set a unique password.
- Turn off remote access to your devices so that they are not open for unauthorised access by others.
- Research a new product before you connect it to the internet. There may already be security vulnerabilities that the manufacturer is aware of. Apply any patches to repair these before connecting it to the internet.
As you can see, sharing is not necessarily caring. The unlimited power of a botnet can give cyber criminals endless possibilities to scam individuals and businesses. There are simple measures you can implement today to keep your system clean. Make sure your computer isn’t doing cyber criminals’ dirty work for them. Ready your defenses today!
Emsisoft Enterprise Security + EDR
Robust and proven endpoint security solution for organizations of all sizes. Start free trialHave a nice (malware-free) day!