New in 2021.10: Introducing MITRE ATT&CK malware behavior patterns

New support for MITRE ATT&CK behavior patterns
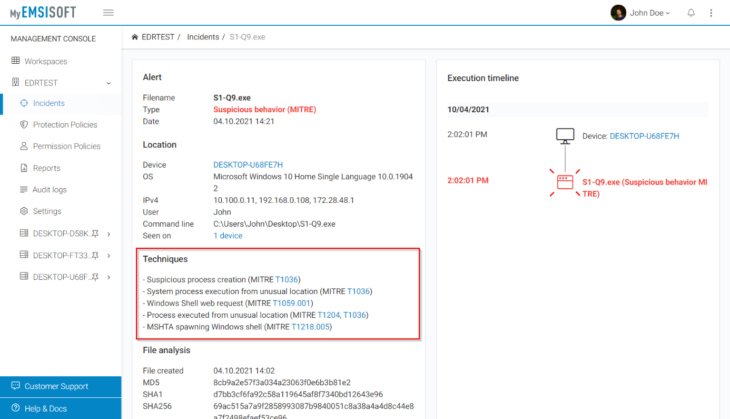
MITRE ATT&CK is a public knowledge base of adversary tactics and techniques. It allows standardized classification of malware behavior patterns. More information here.
The new Incidents panel in MyEmsisoft now provides information on which behavior patterns are used by alerted threats. While not all MITRE ATT&CK patterns apply to endpoints, many do. With this month’s release, we are adding an initial set of 7 supported malware tactics. Over the next few months, we plan to add support for more than 100 of them to cover the entire spectrum of endpoint security-related threats.
When you open an Incident in your workspace you will see which MITRE ATT&CK tactics were found in the alerted process.
Please note that this feature is only available in Emsisoft Business Security and Emsisoft Enterprise Security plans. Compare editions.
All 2021.10 improvements in a nutshell
Device protection (desktop)
- As of version 2021.10, we have ended support for operating systems older than Windows 10 and also ended support for non-64-bit systems. Installations on non-supported systems will stay on version 2021.9 and no longer receive software updates but will continue to receive malware detection updates until June 2022.
- New UI customization feature to disable workspace management controls on devices.
- Several minor tweaks and fixes.
Management console (web app)
- New UI customization feature to disable workspace management controls on devices (via protection policies).
- Several minor tweaks and fixes.
How to obtain the new version
As always, so long as you have auto-updates enabled in the software, you will receive the latest version automatically during your regularly scheduled updates, which are hourly by default.
Note to Enterprise users: If you have chosen to receive “Delayed” updates in the Update settings for your clients, they will receive the new software version no earlier than 30 days after the regular “Stable” availability. This gives you time to perform internal compatibility tests before a new version gets rolled out to your clients automatically.
Have a great and well-protected day!
Emsisoft Enterprise Security + EDR
Robust and proven endpoint security solution for organizations of all sizes. Start free trial