New Cryptolocker copycat PClock2 discovered that targets over 2,500 file extensions

One of the biggest ransomware threats of the last few years, Cryptolocker, was discovered in late 2013. It has been reported that the makers of Cryptolocker made approximately USD$30 million in the first 100 days of operation, and it therefore is no surprise that many variants and copycats emerge that try to capitalize on Cryptolocker’s reputation. Earlier this year, we discovered a Cryptolocker copycat named PClock, for which we developed a decrypter to help victims get their files back without paying the ransom. Now, a new variant of PClock and another copycat of Cryptolocker has emerged: PClock2.
PClock2 demands 0.5 bitcoin ransom to decrypt files
Like other types of ransomware, the main goal of PClock2 is to encrypt important files on the victim’s system in order to compel them to pay a ransom in return for their files. PClock2 encrypts files using a randomly generated key and the RC4 algorithm. Like most other variants it also demands payment in bitcoin and provides the user with a limited time window to produce it. The malware also falsely proclaims that 0.5 bitcoin (the demanded ransom) is approximately equal to US$ 0 while the accurate conversion amounts to almost US$128.
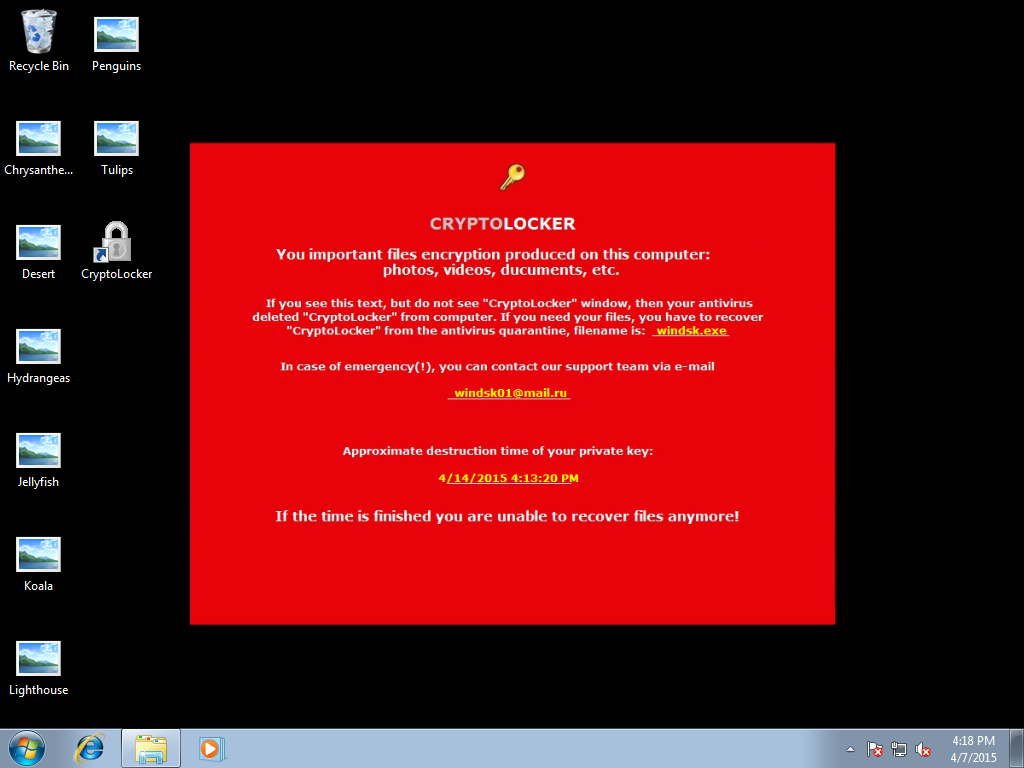
Similar to its predecessor PClock, this variant closely resembles Cryptolocker visually as well:
This malware also recommends users to turn off their antivirus programs in order to save itself from deletion. The application window is clearly meant to threaten and mislead users.
PClock2 behavior and infection methods
PClock2 usually enters the user’s system via infected torrent downloads. Once on a victim’s computer, PClock2 establishes persistence on the system using the following Registry entry:
- [HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun]
“wincl” = “%APPDATA%WinDskwindsk.exe”
PClock2 saves additional details about the infection, like the Bitcoin payment address, here:
- HKEY_CURRENT_USERSoftwareVB and VBA Program SettingsCLOCK
What’s interesting is that PClock2 targets 2583 file extensions which is a lot more compared to earlier types of ransomware we have come across. Since so many different file extensions are targeted, the list became too lengthy to post in this blog post. The command and control servers for this malware are located in these domains:
- http://balanzic.nl
- https://blog.knewmart.com
- http://nrg.facelook.no
- http://www.9188com.com
- http://dota2arcana.com
- http://faceoftopgame.sk
- http://thebatikapartemen.com
- http://www.42kiralama.com
The extracted malware files are stored locally in the following locations:
%APPDATA%WinDskwindsk.exe – The malware executable
%APPDATA%WinDskwindskwp.jpg – The wallpaper generated by the malware
%DESKTOP%CryptoLocker.lnk – A shortcut to the malware executable
%USERPROFILE%enc_files.txt – The list of encrypted files
After encrypting all the files it can find, the ransomware changes the user’s desktop background to this image:
How to recover your files without paying the ransom
Luckily PCLock2 is nowhere near as powerful as it claims to be and none of your files have actually been damaged. Our malware research team has designed a decrypter that will allow you to easily restore your locked files, without paying the ransom. You can download the decrypter here.
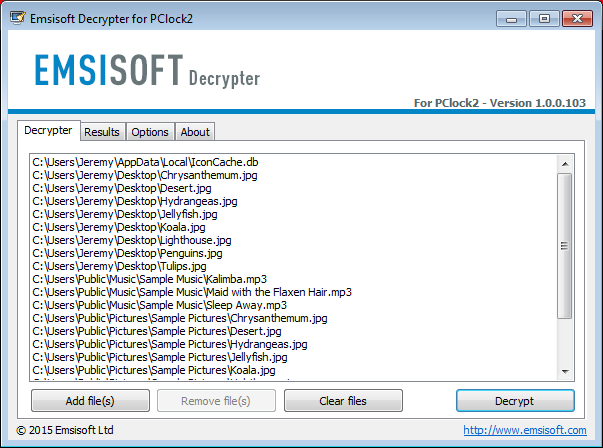
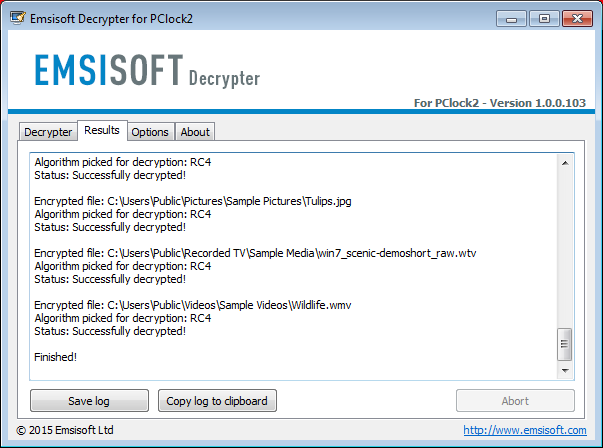
The decryption process is fairly easy as illustrated by these screenshots:
If you don’t feel comfortable performing the decryption process on your own, feel free to create a support request in our support forum or send us an email. We’d appreciate it if you share this post so that more victims of PClock2 can be helped to recover their files.
Prevention is always better than cure which is why we always recommend regular backups and a strong antivirus program that protects you from getting infected in the first place.
Emsisoft Endpoint Protection: Award-Winning Security Made Simple
Experience effortless next-gen technology. Start Free TrialHave a nice (ransomware-free) day!