Emsisoft releases new decryptor for Jigsaw ransomware

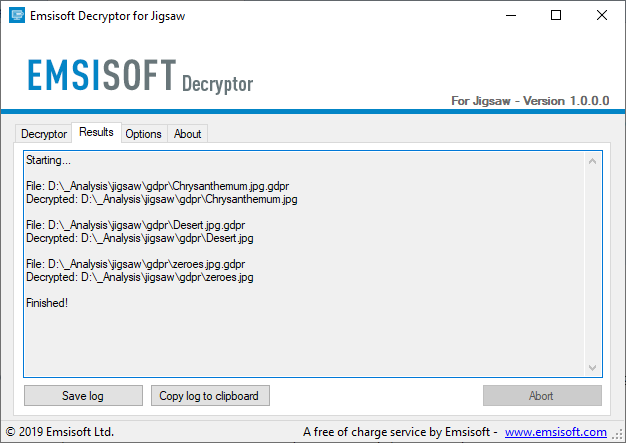
We just released a new free decryption tool for Jigsaw ransomware.
Jigsaw was created in 2016 and known for its “punishment” concept similar to the plot of the popular horror movie franchise, Saw. The movies feature victims that are held hostage, given gruesome escape tools (including the eponymous hacksaw), and suffer dire consequences when puzzles are not solved within a time limit.
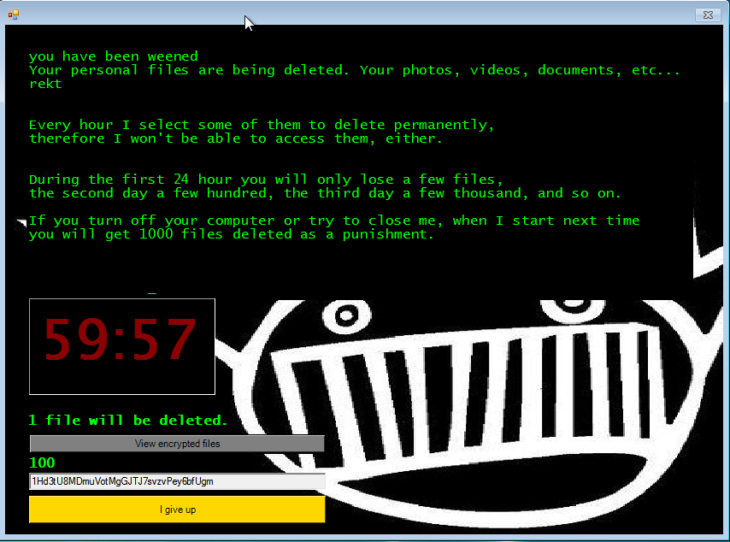
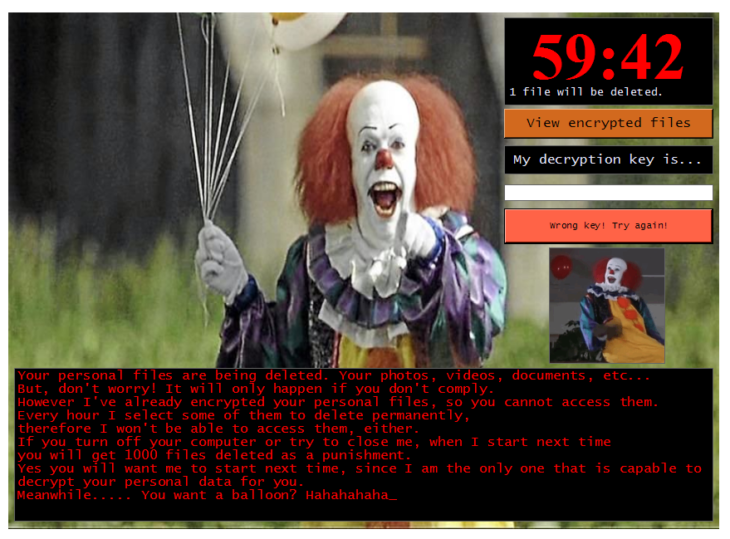
Jigsaw mimics this premise: The ransomware not only encrypts files, it also deletes them on a timed, countdown basis. A single file is deleted an hour after the data has been encrypted and an exponentially increasing number of files are deleted every hour thereafter. After 72 hours, all remaining files are deleted. If the victim reboots or terminates the ransomware’s processes, it will automatically relaunch and delete 1,000 files “as a punishment.”
A decryptor for Jigsaw was released in 2016. Initially, the ransomware was sold on a Tor marketplace, however, it has now been open-sourced which has enabled people to create multiple variants that the original tool could not decrypt. The new tool can currently unlock 85 extensions and will be updated as new variants emerge.
Download the Jigsaw Decryptor here
There are no special requirements needed to use this decryption tool. Users simply need to run the decryptor while online and the decryption process will start. A detailed usage guide is included.
Important: Before you run the decryptor, you first need to:
1. Open Task Manager
2. In the Processes tab, select firefox.exe and drpbx.exe and click “End Task”
3. When that’s done, open MSConfig. Note: The ‘msconfig’ section doesn’t apply to Windows 10. For Windows 10, use task manager’s startup tab instead.
4. In the Startup tab, deselect the startup item firefox.exe that points to %UserProfile%\AppData\Roaming\Frfx\firefox.exe and click OK
Once you’ve completed these steps, you can proceed to run the decryptor.
Technical details
The original 2016 variant posed as a Firefox or Dropbox update and the ransomware GUI featured the image of the character “Billy the Puppet” from the movie Saw.
Jigsaw encrypts victims’ files with AES-128 and appends one of many extensions, including “.fun” and “.game”. A fake error message is displayed to mislead the victim to thinking the ransomware did not run.
Fake error message sample:
GUI samples:
Ransom note sample:
All Your personal files have been AES encrypted. Your photos, videos, documents, etc…
If you look around your PC you cannot access them:)
You must send me $100 USD in bitcoin to the address below if you want your files back.
This expliot will starts out slowly then increases rapidly deleting files
During the first 24 hour you will only lose a few files,
the second day a few hundred, the third day a few thousand, and so on
If you turn off your computer or try to close me, when I start next time.
you will get 900 files deleted as a punishment
I am the only one that is capiable of decyrpting your data contact me via email if you have questions
Only After the bitcoin payment is sent your files will be decrypted
You must buy bitcoin from one of the many exchange sites then send coin too are address below
How too buy bitcoin google search or Check out this link
https://localbitcoins.com/guides/how-to-buy-bitcoins
Now, let’s enjoy our game together
Download the Jigsaw Decryptor here
Emsisoft Endpoint Protection: Award-Winning Security Made Simple
Experience effortless next-gen technology. Start Free TrialRegardless of what any of the Jigsaw ransom notes might say, our decryption tool may be able to help you recover your files for free.